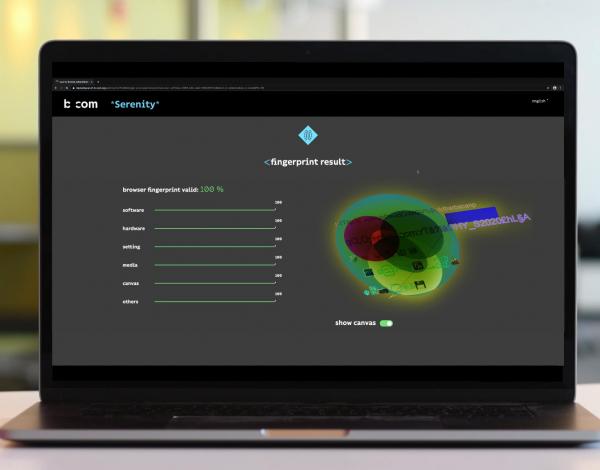
b<>com Serenity
presentation
Multi-factor authentication methods are now essential to access services but are poorly adopted by users due to their extra complexity.
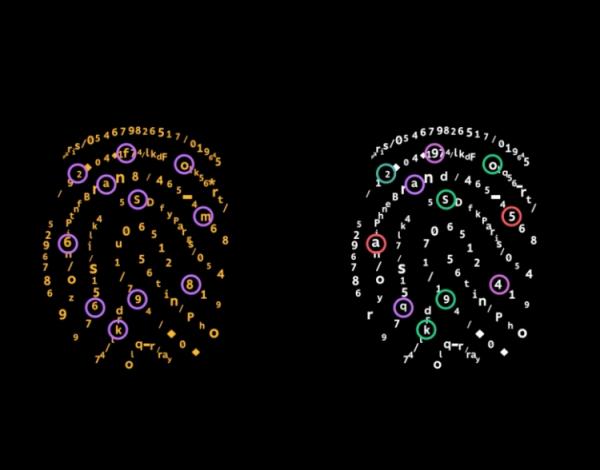
b<>com *Serenity* introduces a new authentication factor based on cutting-edge device fingerprinting techniques.
It adds a transparent layer of protection to authentication processes. By associating a user account with its device’s hardware and software configuration, our approach prevents hackers from re-using login credentials acquired from phishing attacks.
benefits
- Enhance your security with an additional robust and safe authentication factor
- Offer frictionless user experience: transparent, no software installation
- Integrate it easily into any existing access control service as an extra layer of protection
- Lower the TCO of your two-factor authentication solution
features
- Authentication based on login credentials AND users’ devices
- Patented method to prevent spoofing
- Easy to manage devices linked to an account
- OS agnostic and compatible with most popular Internet browsers
- SDK available for Android Apps

Strengthen your authentication solution in a way that's transparent to the user, without needing a password, with the help of a single digital fingerprint for all your devices.
Internet services
Subscription services to multimedia contents and account sharing detection
Asset management
Fraud detection and prevention services
Banking
a new demo of b<>com *Serenity* is available!
It offers you the opportunity to discover why *Serenity* is THE solution to fight against data hacking in such crucial fields as healthcare, and especially in the hospital environment.
Use the form at the bottom of the page to request it.